|
|
IMF Tune - Bringing Back the Exchange Connection Filter
Blocking Spam Spoofing Our Own DomainAre you receiving spam claiming to be from your domain? Today we see how we can counter such spam, turning spoofing to our advantage. A number of technologies blocking email sender spoofing are available. Exchange 2003 and 2007 include the Sender ID filter for this purpose. Querying SPF DNS records, Sender ID is able to block some of the spoofed emails. Despite the usefulness of Sender ID, we observed that a much simpler and lightweight filtering technique could be employed without involving any time consuming DNS queries. Note that here we are not dealing with all possible types of email spoofing. Instead our focus is on emails that spoof our own domain, where we appear to be both the sender and recipient of the spam email.
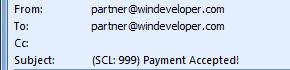
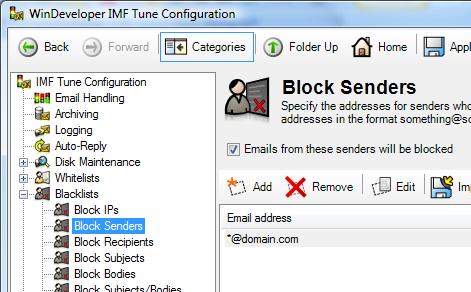
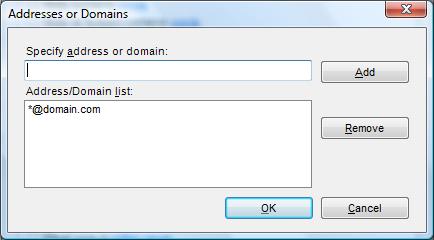
Blacklisting Your Own DomainA very simple but powerful filter that could be employed is sender blacklisting. In IMF Tune we can simply enter our domain in the sender blacklist as follows:
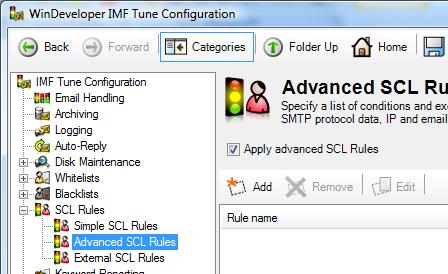
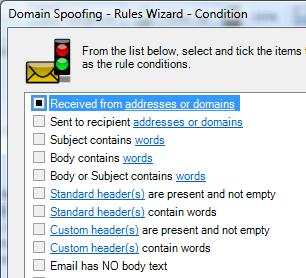
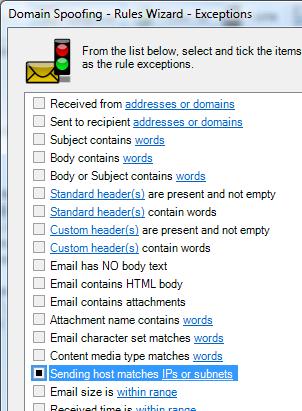
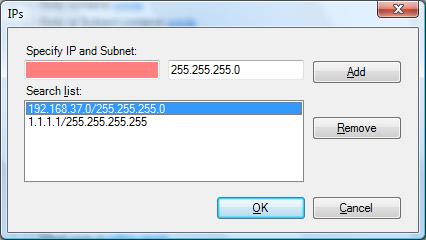
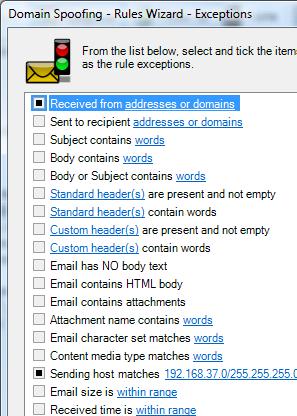
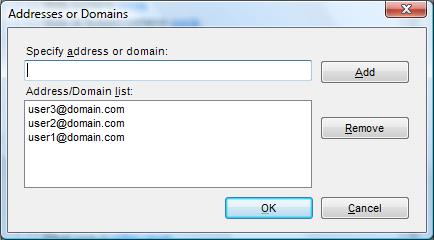
This will block all emails claiming to be from our domain. Such a filter may be readily employed at many organizations with zero false positives. This is due to the simple reason that very often there exists no legitimate reason for an internet originating email to claim to be from our own domain. This is especially true when considering that IMF Tune by default only processes emails originating from the internet over anonymous (un-authenticated) connections. Such a filter does not affect users sending outbound emails or anyone accessing emails over authenticated connections. More Selective Blacklisting Using Advanced SCL RulesAlthough the simple blacklist might do the job, sometimes we have to cater for exceptions. There might be some legitimate hosts that use our domain at the sender to submit inbound emails over anonymous connections. For example an organization might be running applications that generate such emails for reporting purposes. Typical applications include monitoring, accounting and fax-to-email gateways. In addition there might also be some senders that specifically need to be excluded from such a blacklist. In these cases instead of the simple blacklist, we employ an Advanced SCL Rule to build a more selective filter.
|